The term quantum encryption is a mind-boggling mouthful, even in this tech-driven era. What exactly does it even mean? Sometimes called quantum cryptography, this term basically describes a new method for securing data. Quantum cryptography can be thought of as the next iteration in what information technology experts are now calling the quantum arms race – the head-to-head competition between government and the private sector to invent the first mainstream quantum computer.
At the same time, hackers are hard at work preparing to use this quantum computer technology to decrypt data at rates never before seen in the history of computing. It is a tense state of affairs which will impact every private citizen, every business and every government entity all around the world. In this article, learn what quantum encryption is, what it does, how it works and how it can be used to safeguard information vital to the success of your business.
What Is Quantum Cryptography?

Img source: thesslstore.com
Before you can understand how valuable quantum encryption can be to your business. First it is necessary and helpful to develop a working knowledge of what quantum cryptology is and exactly what this term means. The word “quantum” is a term borrowed from the related field of quantum mechanics. This field investigates and works with the very smallest things – such as atoms, electrons, particles of light called photons.
Cryptography, or encryption, is a term borrowed from the field of information technology security that refers to code-making and code-breaking. So, when these two terms are paired, the meaning is one of using very small things (photons made of light) to protect other very small things (bits of data).
Quantum Cryptography Versus “Regular” Encryption
So, what exactly is the difference between this new type of advanced encryption and regular data encryption that is in widespread use today? The current mainstream data encryption standards encryption uses mathematical principles based on factoring and prime numbers. There are two methods in use: symmetric (private key) and asymmetric (public key). Both systems use a system of binary numbers (1, 0) with a single (public key) or dual (private key) decryption code system.
Up until now, both types of data encryption have been relatively hack-resilient, if not completely hack-proof. But with the introduction of mainstream quantum computing now imminent on the horizon, even the most complex mathematical factoring operations will be the work of a moment in the hands of such a massive quantum computer “brain.” So, the industry is overdue for a massive security upgrade, which is coming in the form of quantum cryptography technology.
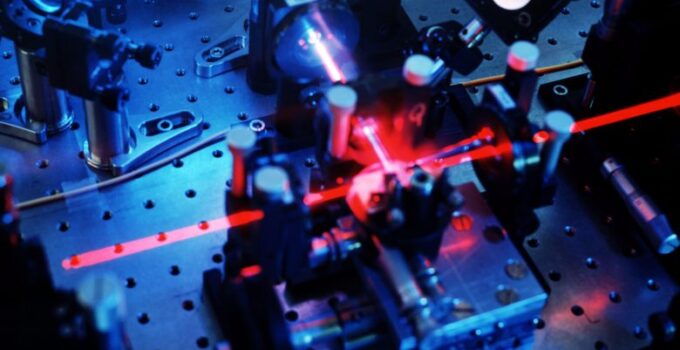
How Does Quantum Cryptography Work?

Img source: cloudessentials.com
This new breed of data encryption turns from math to physics to secure data in transit in ways that are virtually unhackable. To do this, quantum cryptography harnesses the inherently variable behavior of tiny photons of light that serve as carriers for tiny bits of data. These tiny photons have unique properties that make their behavior unbelievably hard to predict – and what cannot be predicted in advance is consequently unbelievably difficult to decrypt.
These tiny light photons can be in more than one place simultaneously. They can be in more than one state simultaneously. They are instantly changed if exposed to any kind of polarizing influence, such as a filter. And they are changed in such a way that the sender and receiver know that they have been changed and thus know that their data transmission has been compromised (i.e., an attempt has been made to decrypt or hack it while in transit).
How Quantum Cryptography Works to Protect Data: Step by Step
Here is a hypothetical example of exactly what quantum cryptology looks like in action. Say Person A wants to send data to Person B. Person A uses a quantum cryptology process called QKD (quantum key distribution) to package up the data, so it is ready to go.
First, each little data bit is attached to a little light photon carrier particle. The entire data package is then sent through a filter called a “polarizer” on its way out the door. The polarizer assigns one of four types of polarization randomly to each photon and its data package. With that done, the data package is sent speeding along a fiber optic cable (or very occasionally, a satellite transmission) to its destination.

Img source: cispa.saarland
At the other end, Person B receives the data package. But before Person B opens it, the photons and their data bits get sent through a type of data reader called a “beam splitter” which can read all four types of polarization. The data bits and their photons are then sent to the right categories of polarizations to await processing.
In the meantime, the beam splitter is also scanning the photons and data bits for interference. If the photons were exposed to any additional polarization along their route, the beam splitter would detect and flag it. This will tell Person B the data has been compromised and the entire message will be discarded.
If no interference is detected, the beam splitter sorts out all the photons, keeping only those that relate to the original QKD. These photons represent the decryption key that allows Person B (and only Person B) to unlock, decrypt and receive Person A’s message.
How Can Quantum Cryptology Protect and Support Your Business?
If all of that was as clear as mud, you are definitely not alone. In fact, when QKD processes are working as they should, it will not be necessary to get a degree in physics to understand how to protect your company’s sensitive data.
But it is necessary to at least have a working basic knowledge of the difference between today’s mathematics-based, binary, factoring-based encryption and tomorrow’s physics-based, unpredictable and virtually unhackable encryption technology to understand why your business needs it. Now let’s take a closer look at how quantum key distribution and encryption can be used to secure your business’s future.
Opens Up New Markets

Img source: rockmountaintech.com
Data security concern continues to be a significant barrier for some customers who are reluctant to shop and make purchases online. By offering secure quantum cryptology data transmission to these customers, your business is able to access new markets and grow your customer base ahead of your competition.
Better Trend Forecasting
Quantum computing technology from companies such as CrownSterling.io can do a lot more than simply protect your company’s most sensitive data. This advanced physics-based technology can also rapidly make sense of huge amounts of seemingly unrelated data by analyzing for patterns to predict future trends and new market openings.
This technology has applications in nearly every area of business operation, from predicting the weather to analyzing the terrain to decoding traffic patterns to identifying emerging customers’ wants and needs. If you want to learn more about quantum computing and its possibilities check Techslang.
Improved Automation Opportunities
Every forward step in automation frees up valuable time, energy and money to redirect in profitable, productive ways. The ability to encrypt, transmit and analyze data at an unprecedented rate and with a virtually unhackable level of security speeds up business optimization, reduces overhead, boosts profits and widens the gap between your company and its primary competitors. In every way, quantum cryptology positions your company for future profitable success.